Incident Response Vulnerability Management: Finding and Fixing the Open Door
In more than a third of the destructive attacks we have helped customers recover from, whether ransomware encryption or data wiping by a nation-state actor or its proxy, the initial access vector was an exploited vulnerability. Restoring systems without first addressing the attack surface that enabled the compromise is like replacing stolen jewellery after a burglary, then heading out the next day having left the door open and the alarm switched off.
When a ransomware or wiper attack hits, vulnerability management stops being a hygiene exercise and becomes a survival function. The question is no longer “what should we patch in our next cycle?” , it becomes “what allowed this attack to happen and how do we ensure it cannot happen again before we bring the business back online?”
This is where many recoveries after a destructive cyberattack fail: organisations focus on recovery speed, but neglect attack surface reduction during the response itself. The result is predictable: they recover into the same conditions that enabled the compromise in the first place.
Why Attack Surface Discovery at the Point of Impact Matters
If you want to identify patient zero, you need to understand the attack surface as it existed at the moment of compromise, not as it looks today. That distinction is critical because attackers:
Disable or evade endpoint security tooling like End-point Detection and Response
Remove artefacts
Clear logs
Modify configurations
Introduce persistence mechanisms
By the time you start investigating, your environment is already a distorted version of Business-as-Usual reality. This is why having the ability to reconstruct attack surface at the point of attack is essential:
It allows you to identify the initial entry vector
It exposes unpatched or misconfigured assets that were actually exploitable
It helps distinguish cause vs. consequence, in other words what enabled the breach vs. what changed after it
Think of you compromised systems like a crime scene: if you only look for evidence has been cleaned, you are working from assumptions rather than evidence.
Vulnerabilities Are Not Just “Unpatched Systems”
Another common failure during incident response is treating vulnerability management as synonymous with “missing patches”. In reality, vulnerabilities can exist across multiple layers:
Applications, both Web and native applications
Libraries
Operating Systems
Middleware
Configuration and Architecture
Human, in the case of Social Engineering but this one is beyond the scope of this post!
In many of the incidents I’ve been involved in, the root cause is rarely a single vulnerability. It is a vulnerability chain of multiple weaknesses across systems identities, and configurations that allows the attack to progress from initial access through to full impact. If you only fix one link in that chain, the adversary may still have paths back in.
How to Discover Vulnerabilities During Incident Response
Discovery during an active incident is fundamentally different from routine scanning, you’re not trying to build a complete inventory, you are instead trying to identify what mattered to the attacker. Some techniques you can use to achieve this:
Backup Snapshot-Based Analysis
Focus on high-probability entry points, prioritising internet-facing assets and identity infrastructure. Leverage backup snapshots to:
Reconstruct systems at multiple points in time,. Modern backup platforms like Cohesity allow you to instantiate snapshots on the backup platform itself so that they can be scanned by a vulnerability scanner, Cohesity SnapTree allows instant, zero-cost clones to be used for this purpose.
Compare pre- and post-compromise states, by using this ability to stand up instant clones of snapshots before and after the attack.
This gives you something most security tools cannot: time-series visibility.
Forensic Triage of Patient Zero Using Backup
Identify the initial compromised host(s) and time of initial compromise.
Use the backup platform to instantiate a clone of the snapshot for that time and examine exposed services, patch levels and configurations.
Review local logs (including those never forwarded to SIEM) of the instantiated clone.
Configuration & Identity Review
Using the instantiated clones from the backup platform:
Audit privilege assignments.
Identify misconfigurations in IAM, AD or cloud control planes.
Building a Remediation Plan Under Fire
Remediation during incident response is not about patch completeness, it is about risk reduction aligned to recovery sequencing and impact tolerances.
Prioritise Entry Points First
Close the initial access vector
Patch or isolate exposed services
Remove Persistence Mechanisms
Rebuild Trust in Identity
Reset credentials
Re-establish privileged access controls
Validate directory integrity
Sequence Remediation with Recovery
Do not repatriate systems until their vulnerabilities are addressed
Align remediation with Minimum Viable Company priorities
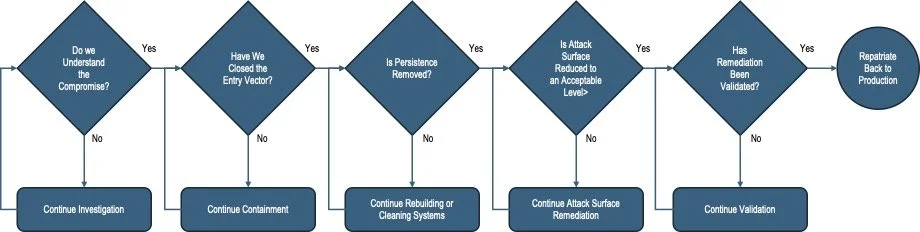
Decision Gates During the Response & Recovery Process
This is where operational discipline matters, you need explicit decision gates:
Validating Remediation Using a Backup Platform
This is where modern data management platforms become a security control, not just a recovery tool. They allow you to validate remediation in a Clean Room, a controlled, isolated environment:
Mount historical snapshots for comparison
Scan restored systems for vulnerabilities
Perform malware analysis and sandboxing
Validate configuration changes
Test patched systems before production release
The Clean Room allows you to validate without trusting the compromised environment., this removes a major source of uncertainty during incident response.
Putting it all together
In a nutshell:
Ingest trusted backup data into the clean room
Use backup snapshots to reconstruct systems at relevant points in time
Perform vulnerability discovery and forensic analysis
Apply remediation (patching, configuration changes, rebuilds)
Validate systems in the clean room
Promote trusted, validated systems back into production
The clean room becomes the bridge between compromise (dirty) and trusted (clean) state.
Most organisations can restore data faster than they can restore trust, vulnerability management during incident response is how you close that gap.
If you do it vulnerability management well, you don’t just recover, you come back stronger, with a reduced attack surface and a better understanding of how your organisation actually operates under pressure. Do it badly, and you are not solving the problem at all, merely winding the clock back a minute to midnight and hoping it does not strike again.